Batch strategy Vector search compares query users (N, the users we’re targeting) against base users (M, the...
Cloud
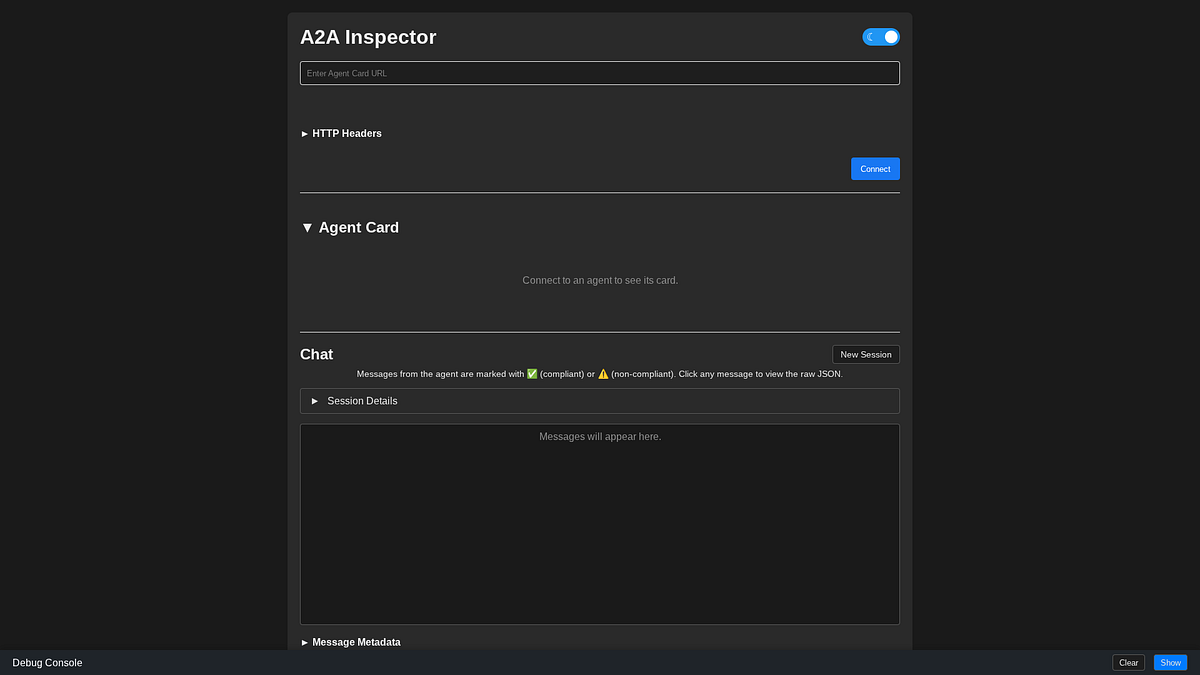
Deep Dive on the A2A Protocol with the Python ADK This tutorial aims to build starter “Hello...
Cloud infrastructure reliability is foundational, yet even the most sophisticated global networks can suffer from a critical...
Secrets access To access the the Gemma 3 model from Keras Hub, you will need to provide...
Choosing the right route As we planned the move to a microservices-based backend, we evaluated our options,...
Use Case: Transforming Retail Logs into Customer Insights Let’s stop looking at snippets and build something real....
Today, we’re announcing the general availability of provisioned mode for AWS Lambda with Amazon Simple Queue Service...
With the pace of scientific discovery moving faster than ever, we’re excited to join the supercomputing community...
If you want to upgrade from a Free Trial account and keep the credits amount, you should...
Building confidence through validated integrations As part of the Google Unified Security Recommended program, partners agree to...