Automating code reviews with AI can dramatically speed up your team’s development cycle. However, the reality is that many development teams manage code securely behind a corporate firewall. Relying on public-facing SaaS bots is often a non-starter.
This guide walks through configuring the run-gemini-cli GitHub Action to execute these reviews securely within a self-hosted GitHub Enterprise Server or GHES environment. By the way, code review is just one of many potential use cases. Whether your goal is drafting documentation, enforcing architectural standards, or summarizing diffs, the setup described here remains exactly the same.
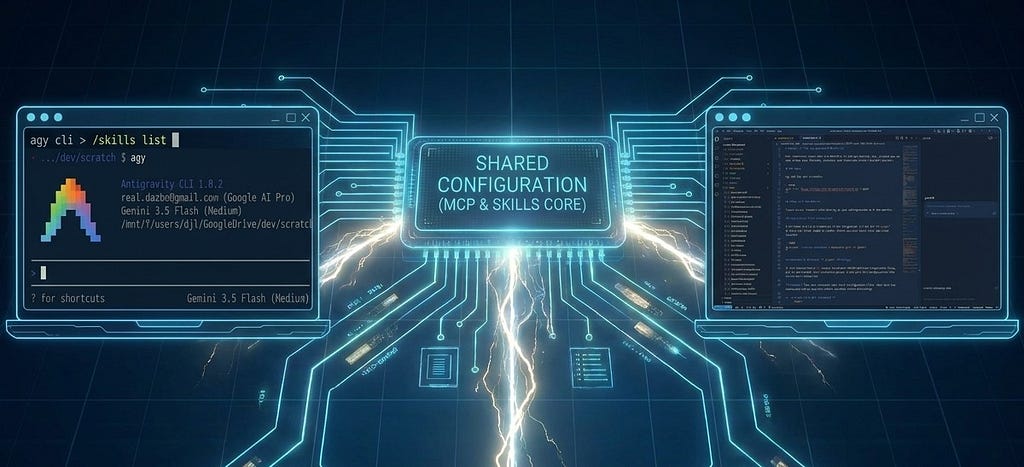
Architecture Overview
The Gemini CLI uses an MCP server running inside an ephemeral Docker container. This server handles authentication with the GitHub API, reads pull request data, and posts review comments back to the repository.
While the default action works smoothly out-of-the-box with public github.com endpoints, bringing it into a GHES instance requires a few targeted environment overrides. Specifically, you’ll need to explicitly handle self-hosted runner execution, map out your custom domain routing, navigate your internal root Certificate Authorities, and route Enterprise Personal Access Tokens properly.

Configuration Steps
Configure the self-hosted runner
First, the GitHub Action must execute on hardware provisioned within your enterprise network. Update the workflow YAML to specify your self-hosted runner labels.
jobs:
triage:
runs-on: ['self-hosted']
Override the base URL routing
By default, the internal CLI components attempt to resolve api.github.com. To ensure the MCP server targets your endpoint instead, you must extract the enterprise instance’s base URL and inject it into the execution environment.
steps:
- name: 'Initialize runner environment'
run: |-
# Secure the config directory to prevent initialization errors
mkdir -p ~/.gemini
echo '{"projects":{}}' > ~/.gemini/projects.json
# Dynamically extract and assign the internal hostname
GH_HOST="${GITHUB_SERVER_URL#https://}"
echo "GH_HOST=${GH_HOST#http://}" >> "${GITHUB_ENV}"
This dynamically maps the default GITHUB_SERVER_URL into a format the agent can process.
Handle internal TLS certificates
If your instance administrator has configured a custom TLS certificate using an internal corporate CA for GHES, you’ll need the Node.js runtime powering the MCP container to recognize it. The Node.js runtime does not inherently trust the host operating system’s certificate store out of the box.
If you see self-signed certificate in certificate chain errors during API callbacks, you’ll need to address this. The secure approach is to map your internal CA bundle into the environment and utilize the NODE_EXTRA_CA_CERTS environment variable to explicitly trust your corporate certificates. As a workaround for testing, you can configure the Node.js runtime to bypass TLS verification with the following environment variable parameter:
"env": {
"NODE_TLS_REJECT_UNAUTHORIZED": "0"
}
Final Thoughts
Once you’ve configured your GitHub Actions workflow, the code review process is smooth. New pull requests will trigger code reviews, and Gemini’s findings will show up as comments directly on the PR.
Ready to bring intelligent code review into your own secure environment? I’d recommend starting by examining the run-gemini-cli repository.
Are you using the Gemini CLI in creative ways? I’d love to hear from you. Let’s keep the conversation going on X, LinkedIn, or Bluesky.
AI Code Reviews with Gemini CLI on GitHub Enterprise Server was originally published in Google Cloud – Community on Medium, where people are continuing the conversation by highlighting and responding to this story.
Source Credit: https://medium.com/google-cloud/ai-code-reviews-with-gemini-cli-on-github-enterprise-server-c21ea56da074?source=rss—-e52cf94d98af—4